Rolling-PWN — Coursework Study
Disclaimer
This document is a university coursework assignment, translated and summarized from the original German version using ChatGPT.
It is not peer-reviewed and not formally published.
Provided for educational and demonstrational purposes only.
Author: skull
Keywords: Rolling Code, Keyless Entry, Rolling-PWN, Car Key Fobs, CAN-Bus, Replay Attack
ABSTRACT
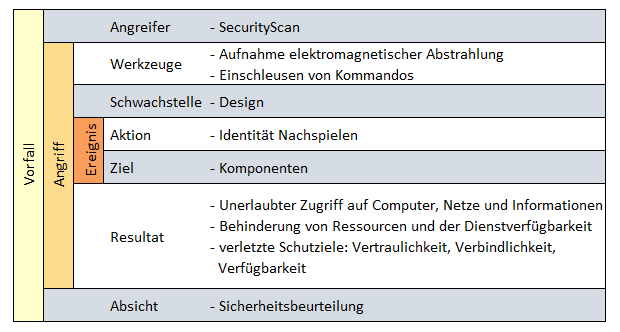
This coursework analyzes the Rolling-PWN attack on modern keyless entry systems in vehicles.
It explains the technical foundations, describes the attack in detail, and discusses potential countermeasures.
1. INTRODUCTION
With the widespread adoption of keyless entry systems, the attack surface for vehicles has expanded significantly.
Replay and rolling-code attacks pose serious threats, with Rolling-PWN being a recent high-profile example.
The objective of this coursework is to analyze the attack model, document its workflow, and evaluate its real-world impact.
2. TECHNICAL BACKGROUND
2.1 Keyless Entry Systems
Keyless entry allows unlocking and starting a car without pressing a button on the key fob.
Communication occurs over radio protocols and is typically encrypted.
2.2 Rolling Codes
To mitigate replay attacks, rolling codes are used.
Each transmitted code is unique and valid only once, with the next code derived from a pseudo-random sequence.
3. THE ROLLING-PWN ATTACK
3.1 Attack Workflow
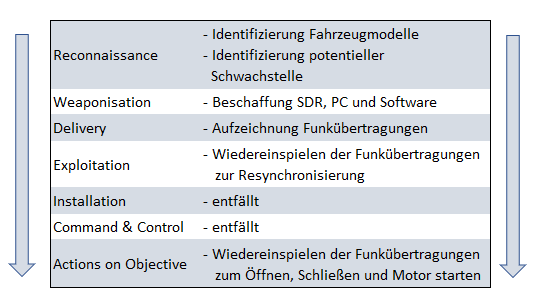
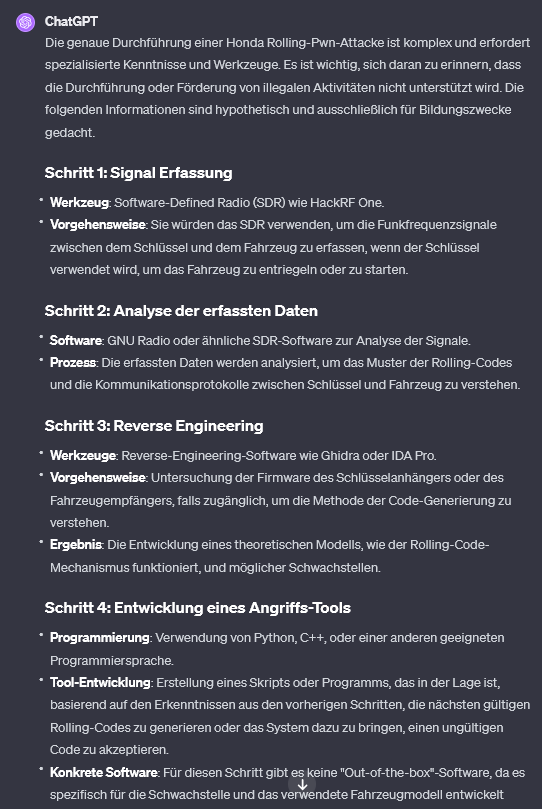
The Rolling-PWN attack exploits weaknesses in rolling-code implementations.
By capturing and replaying signals, attackers can open a vehicle without possessing the legitimate key.
Steps:
- Signal Capture: Record a key fob transmission when the user unlocks the vehicle.
- Analysis: Inspect the captured rolling code.
- Replay: Transmit the code later to unlock the car.
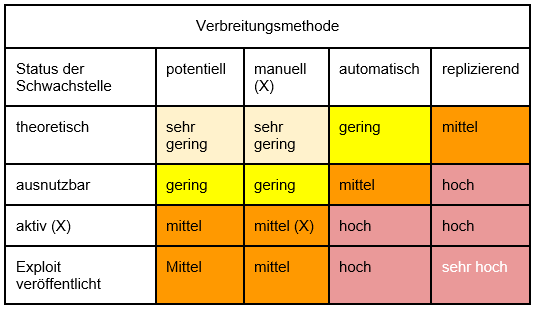
3.2 Vulnerability
If the vehicle’s ECU/BCM does not strictly validate that the received code is the immediate next value in the rolling sequence, replayed signals can “advance” the counter.
This flaw allows multiple successful replays.
4. EXPERIMENTAL REPLICATION
To illustrate the concept, a Software Defined Radio (SDR) and a simple rolling-code key fob (433 MHz) were used.
4.1 Setup
4.2 Results
- Signals were captured and decoded with SDR software.
- A replayed code successfully unlocked the test system.
5. DISCUSSION
5.1 Range and Accessibility
- No physical access to the vehicle is required.
- Low cost: SDR hardware and open-source software are sufficient.
5.2 Consequences
- Unauthorized unlocking (and in some cases starting) of vehicles.
- Rolling codes, when poorly implemented, do not prevent replay attacks.
6. COUNTERMEASURES
Recommended defenses include:
- Stronger cryptographic challenge-response mechanisms.
- Stricter validation windows for rolling codes.
- Regular firmware and ECU updates.
Manufacturers should periodically test and update their implementations.
7. CONCLUSION
The Rolling-PWN attack highlights the importance of correct implementation, even with proven security mechanisms.
Continuous testing, penetration assessments, and timely patching are essential to maintain resilience against such attacks.
REFERENCES
- Original Rolling-PWN Whitepaper
- Heise: Rolling-PWN – New Attack on Car Key Fobs
- Wikipedia: Keyless Go
- Wikipedia: Rolling Code
- USENIX 2008: Practical Attacks Against Rolling Code Systems
- RTL-SDR Basics
- CAN-Bus Security Research
- NDR: Car Key Hack
For feedback or questions, contact: 📧 skull@ttl.zip